-
Posted On Uncategorized
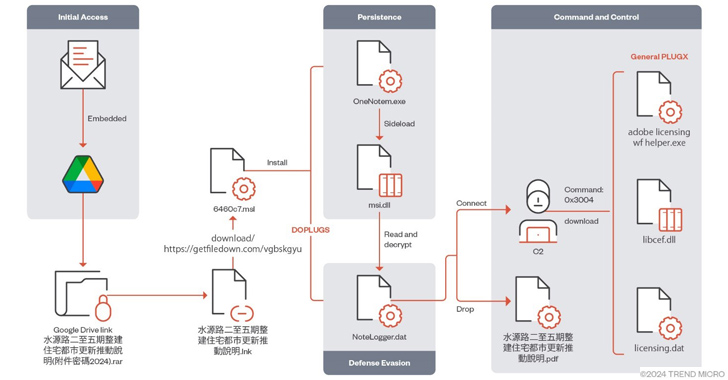
Mustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS


The China-linked threat actor known as Mustang Panda has targeted various Asian countries using a variant of the PlugX (aka…
-
Posted On Uncategorized
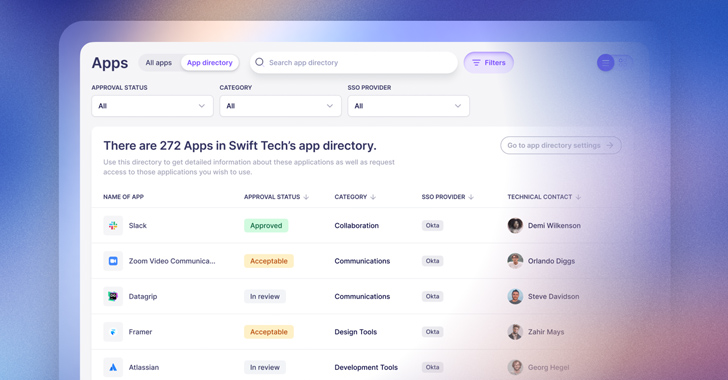
6 Ways to Simplify SaaS Identity Governance


With SaaS applications now making up the vast majority of technology used by employees in most organizations, tasks related to…
-
Posted On Uncategorized
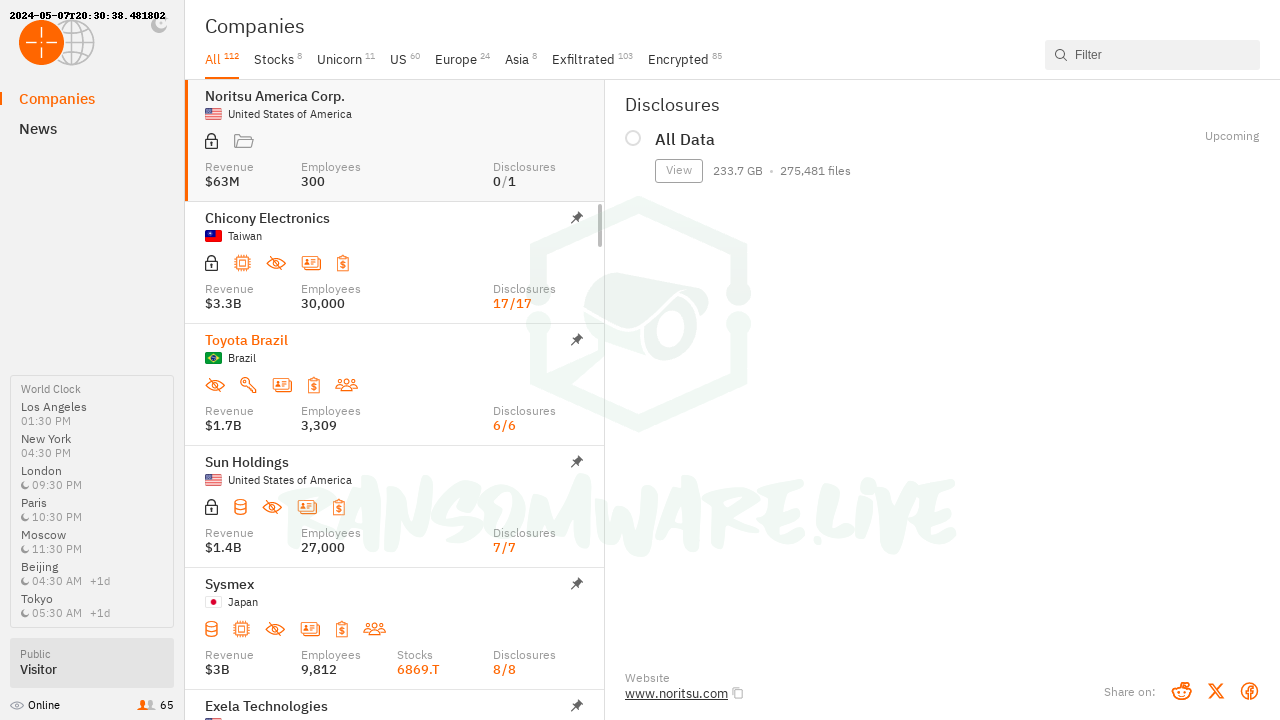
Hackers using stolen credentials to launch attacks as info-stealing peaks


Attackers prefer compromised valid accounts over phishing or any other infection methods to gain access into victim environments, according to…
-
Posted On Uncategorized
Navigating the Maze: Tips to Consider When Choosing SOC as a Service


Choosing the right SOC as a Service (SOCaaS) is crucial for businesses aiming to strengthen their cyber defenses. This decision…
-
Posted On Uncategorized
VMware Highlights Critical Flaws in Enhanced Authentication Plug-in (EAP)


In a recent security advisory, VMware has urgently recommended the removal of the enhanced authentication plug-in (EAP) due to the…
-
Posted On Uncategorized
Cybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery


On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were…
-
Posted On Uncategorized
NSA Cyber Director Rob Joyce Retires After 34 Years of Service


NSA veteran Rob Joyce retires from the post of director, scheduled for the end of March, marking the culmination of…
-
Posted On Uncategorized
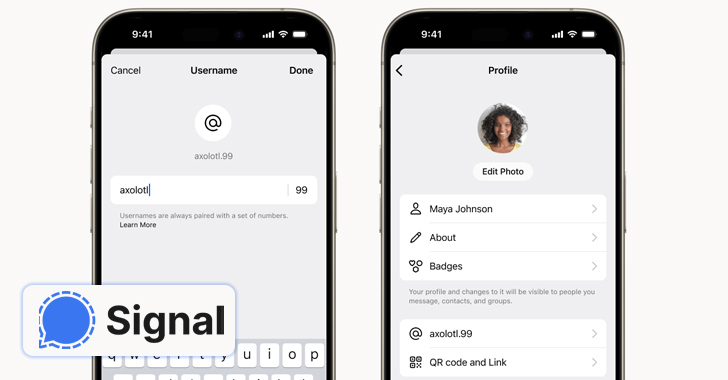
Signal Introduces Usernames, Allowing Users to Keep Their Phone Numbers Private


End-to-end encrypted (E2EE) messaging app Signal said it’s piloting a new feature that allows users to create unique usernames (not…