-
Posted On Uncategorized
🏴☠️ Metaencryptor has just published a new victim : Max Wild GmbH


Max Wild GmbH, based in Berkheim, has been responsible for the professional and sustainable implementation of numerous services in the…
-
Posted On Uncategorized
🏴☠️ Abyss has just published a new victim : woldae.com


woldae.com 9.7Tb uncompressed data
-
Posted On Uncategorized
Russian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator


The U.K. National Crime Agency (NCA) has unmasked the administrator and developer of the LockBit ransomware operation, revealing it to…
-
Posted On Uncategorized
Global Cyber Crime Crackdown: LockBit Ransomware Leader Unmasked and Sanctioned


In a landmark international operation, Dmitry Khoroshev, the once-anonymous leader behind the notorious LockBit Ransomware gang has been unmasked and…
-
Posted On Uncategorized
🏴☠️ Medusa has just published a new victim : Chemring Group


Chemring Group is a global business providing a range of advanced technology products and services to the aerospace, defence and…
-
Posted On Uncategorized
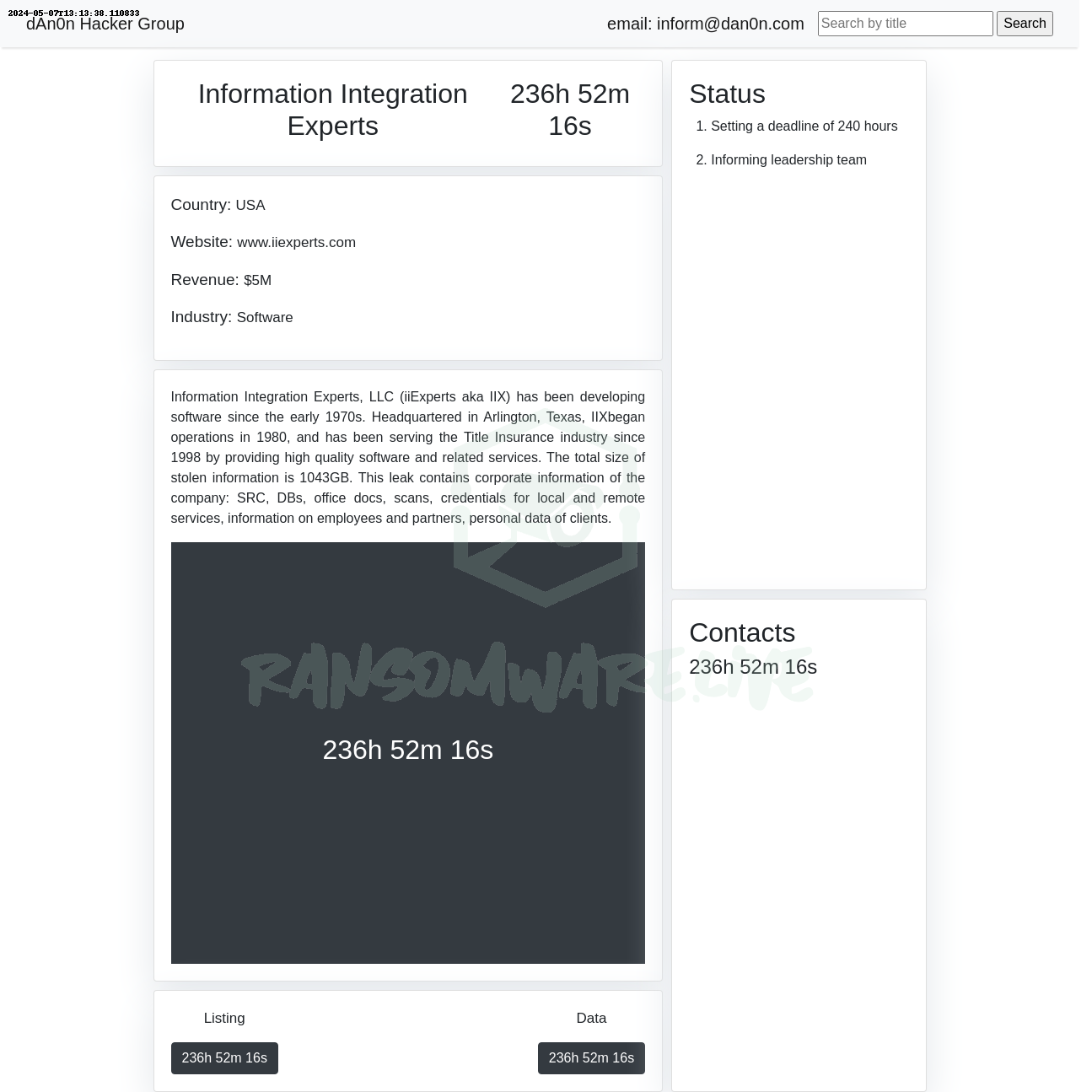
🏴☠️ Dan0n has just published a new victim : Information Integration Experts


Information Integration Experts, LLC (iiExperts aka IIX) has been developing software since the early 1970s. Headquartered in Arlington, Texas, IIXbegan…
-
Posted On Uncategorized
China-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion


The MITRE Corporation has offered more details into the recently disclosed cyber attack, stating that the first evidence of the…
-
Posted On Uncategorized
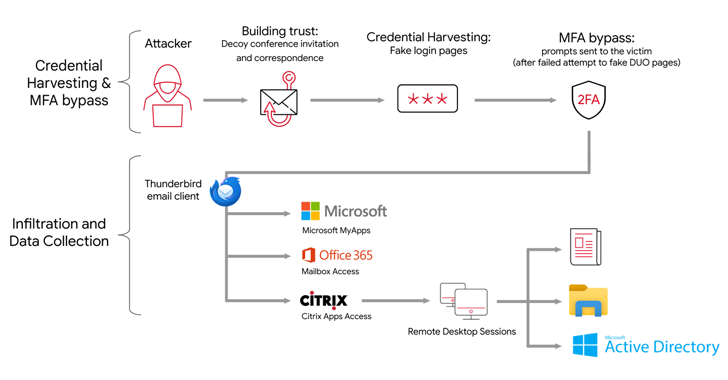
APT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data


The Iranian state-backed hacking outfit called APT42 is making use of enhanced social engineering schemes to infiltrate target networks and cloud environments. Targets of…